Penetration Tester
Security Researcher
Documenting offensive security research, red team tradecraft, and privacy analysis. All operations are authorized. All findings are disclosed responsibly.
└─$ cat latest_posts.txt
 ★ pinned
★ pinned
DOJ charged ex-US intel for UAE spyware. One was ExpressVPN's CIO — revealed one day after Kape bought ExpressVPN for $936M. The adware company that now holds the keys to your traffic.

Timestamps are just metadata — and metadata is incredibly easy to manipulate. Understanding $STANDARD_INFORMATION vs $FILE_NAME and why clumsiness leaves more evidence than doing nothing.

Deleting a file doesn't make it disappear. On HDDs the data stays until overwritten. On modern SSDs with TRIM + encryption, it's usually gone for good. The real story is more nuanced.

Surveillance no longer asks "what did you do?" It asks "what will you do?" Your behavioral fingerprint predicts and pre-judges you before you've acted.
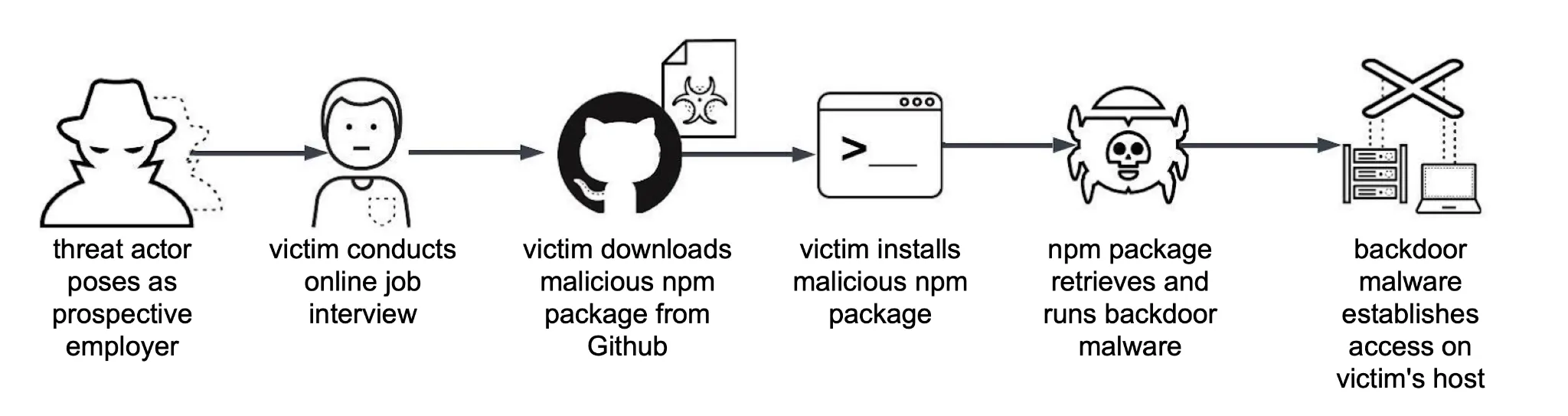
North Korean APT weaponizing fake GitHub job repos. A red team simulation of the full chain — social engineering, XOR-encrypted payloads, and silent C2 via npm postinstall.

A social engineering technique that tricks victims into pasting a disguised PowerShell command into File Explorer. No exploits. No admin rights. Just OS trust and bad habits.
Multi-stage HTA phishing simulation using only native Windows binaries. No implants, no custom executables — just mshta.exe, WScript, PowerShell, and registry persistence.

